Ensuring the resilience of your digital presence requires a sophisticated approach to WordPress hosting security best practices NZ, specifically tailored to the local legal and technical landscape of 2026. This comprehensive guide explores the essential layers of defense needed for Kiwi businesses, from meeting strict data residency requirements under the New Zealand Privacy Act 2020 to implementing advanced server-side hardening techniques like AI-powered malware scanning and Web Application Firewalls (WAF). You will learn how to leverage local Auckland-based infrastructure to satisfy Māori Data Sovereignty principles while maximizing performance through sub-20ms latency. From enforcing multi-factor authentication (MFA) to managing secure off-site backups, this article provide a technical roadmap for developers and business owners to protect their WordPress ecosystems against the evolving threat landscape of Aotearoa.

Strategic Foundations: Why NZ Context Matters for WordPress Security
In 2026, the WordPress hosting security best practices NZ framework is defined by more than just firewalls; it is a matter of digital trust and legal compliance. For New Zealand businesses, the physical location of your server and the jurisdiction governing your data are critical components of your security posture. Hosting your WordPress site in an Auckland-based data centre ensures that sensitive customer information remains under the protection of New Zealand law, simplifying your obligations under the Privacy Act 2020. Furthermore, local infrastructure allows for "secure-by-design" configurations that utilize domestic peering to filter malicious offshore traffic before it even reaches your server's edge.
- Sub-20ms Latency Security: Faster response times allow for more aggressive real-time security scanning without degrading the user experience.
- NZ Privacy Act Compliance: Local hosting keeps data within the reach of the Office of the Privacy Commissioner (OPC), ensuring transparent chain-of-custody for personal info.
- Domestic Threat Intelligence: Top-tier NZ hosts collaborate with CERT NZ to proactively block IP ranges associated with localized phishing and brute-force campaigns.
- Network Isolation: Utilizing local NZ data centres helps isolate your site from massive global DDoS attacks that often target larger international data hubs.
Sub-20ms Latency Security: Faster response times allow for more aggressive real-time security scanning without degrading the user experience.
NZ Privacy Act Compliance: Local hosting keeps data within the reach of the Office of the Privacy Commissioner (OPC), ensuring transparent chain-of-custody for personal info.
Domestic Threat Intelligence: Top-tier NZ hosts collaborate with CERT NZ to proactively block IP ranges associated with localized phishing and brute-force campaigns.
Network Isolation: Utilizing local NZ data centres helps isolate your site from massive global DDoS attacks that often target larger international data hubs.
The Impact of the Privacy Act 2020 on WordPress Sites
The Privacy Act 2020 introduced mandatory breach notification and significant penalties for non-compliance. For WordPress owners, this means that a single successful hack isn't just a technical problem—it's a legal liability. Implementing local WordPress hosting security best practices NZ ensures that your security safeguards meet the "reasonable steps" threshold required by Principle 5 of the Act.
| Security Metric | NZ Standard (2026) | Offshore Risk |
| Data Residency | 100% On-shore NZ | Subject to foreign laws (e.g., US CLOUD Act) |
| Authentication | Enforced MFA for all admins | Often password-only by default |
| Malware Scanning | Daily Real-time AI Scans | Occasional / Manual only |
| Jurisdiction | NZ Privacy Commissioner | Multiple/Conflicting Legal Systems |
Implementing Māori Data Sovereignty in WordPress Hosting
Māori Data Sovereignty (MDS) principles emphasize that data about or from Māori people, culture, and resources should be subject to Māori governance. For NZ-based WordPress sites, this often translates to a requirement that data be stored in Aotearoa to ensure that "Rangatiratanga" (authority) and "Kaitiakitanga" (guardianship) are maintained. By choosing a local host that understands these cultural requirements, you are ensuring that your digital assets are managed according to tikanga Māori principles, which is increasingly essential for Iwi organizations, government agencies, and socially responsible businesses.
- Rangatiratanga (Authority): Decisions about physical data storage shall enhance control for current and future generations of Māori.
- Whakapapa (Relationships): Every piece of data has a genealogy; accurate metadata must track the context and purpose of data collection.
- Whanaungatanga (Obligations): Organizations are accountable to the communities from whom the data derives, requiring transparent security audits.
- Kotahitanga (Collective Benefit): WordPress ecosystems should be designed to benefit Māori communities directly and prevent data stigmatization.
Rangatiratanga (Authority): Decisions about physical data storage shall enhance control for current and future generations of Māori.
Whakapapa (Relationships): Every piece of data has a genealogy; accurate metadata must track the context and purpose of data collection.
Whanaungatanga (Obligations): Organizations are accountable to the communities from whom the data derives, requiring transparent security audits.
Kotahitanga (Collective Benefit): WordPress ecosystems should be designed to benefit Māori communities directly and prevent data stigmatization.
Jurisdiction and Control
Genuine sovereignty means that every engineer with access to your data is employed under New Zealand law, ensuring that no foreign jurisdiction can override local data governance policies. This is a core reason why many NZ entities are migrating away from global hyperscalers and toward sovereign NZ cloud providers for their WordPress hosting.
Essential Server-Level Hardening for NZ WordPress Hosts
The foundation of WordPress hosting security best practices NZ begins at the server level, long before you install a single plugin. A secure host in 2026 must provide containerized environments using tools like CloudLinux to ensure that a security breach on one site does not spread to others on the same physical hardware. Furthermore, the server's PHP and database configurations must be "hardened"—disabling dangerous functions like exec() or shell_exec() and ensuring the database user only has the specific permissions required for WordPress to function.
- Web Application Firewall (WAF): Essential for filtering out SQL injection, Cross-Site Scripting (XSS), and common WordPress exploits at the network edge.
- Account Isolation: Ensuring your site lives in its own "sandbox" with dedicated resources and permissions.
- Secure PHP Configuration: Running the latest stable PHP version (8.3+) with error reporting disabled to prevent information leaks.
- Malware Signatures: Server-level scanners that use AI to detect both known and "zero-day" malware injections.
Web Application Firewall (WAF): Essential for filtering out SQL injection, Cross-Site Scripting (XSS), and common WordPress exploits at the network edge.
Account Isolation: Ensuring your site lives in its own "sandbox" with dedicated resources and permissions.
Secure PHP Configuration: Running the latest stable PHP version (8.3+) with error reporting disabled to prevent information leaks.
Malware Signatures: Server-level scanners that use AI to detect both known and "zero-day" malware injections.
| Hardening Layer | Technology | Primary Benefit |
| OS Level | CloudLinux / CageFS | Prevents cross-site contamination |
| Web Server | LiteSpeed / Nginx Hardening | Mitigates DDoS and protocol attacks |
| Database | Restricted Table Prefixes | Deterrents for SQL injection |
| File System | Read-Only Core Files | Prevents unauthorized file modification |
The Power of Real-Time AI Threat Detection
Modern NZ hosts now utilize AI models like Imunify360 to monitor server traffic in real-time. These systems can identify "human-like" bot behaviors that traditional static firewalls might miss, automatically gray-listing suspicious IPs until they pass a CAPTCHA or other verification.
Enforcing Authentication and Admin Security Protocols
Most WordPress breaches in Aotearoa occur due to leaked credentials or brute-force attacks on the admin login. To combat this, WordPress hosting security best practices NZ mandate moving beyond simple passwords. In 2026, multi-factor authentication (MFA) is the "gold standard," requiring a one-time code from a smartphone app (like Authy or Google Authenticator) in addition to a strong password. Additionally, restricting access to the /wp-admin/ area by IP address ensures that only your trusted staff can even see the login screen.
- Mandatory MFA/2FA: Required for all users with "Administrator" or "Editor" roles to block 99.9% of account takeovers.
- Hide Admin URL: Changing the default /wp-admin/ or wp-login.php path to a custom, secret URL to confuse automated botnets.
- Limit Login Attempts: Automatically locking out any IP address that fails to log in more than 3-5 times.
- Principle of Least Privilege: Only granting users the minimum access levels they need; most staff do not need "Administrator" access.
Mandatory MFA/2FA: Required for all users with "Administrator" or "Editor" roles to block 99.9% of account takeovers.
Hide Admin URL: Changing the default /wp-admin/ or wp-login.php path to a custom, secret URL to confuse automated botnets.
Limit Login Attempts: Automatically locking out any IP address that fails to log in more than 3-5 times.
Principle of Least Privilege: Only granting users the minimum access levels they need; most staff do not need "Administrator" access.
Password Management Excellence
Ditch the post-it notes and reused passwords. A modern security stack includes the use of password managers (like 1Password or Bitwarden) for every team member. These tools ensure that every site password is unique and at least 16-20 characters long, incorporating a random mix of symbols and numbers.

Managing Updates: The #1 Defense Against Kiwi Hacks
The most common reason WordPress sites in New Zealand get hacked is outdated software. Hackers actively scan the .nz domain space for known vulnerabilities in older versions of WordPress core, plugins, and themes. A core pillar of WordPress hosting security best practices NZ is the implementation of a rigorous update routine. This involves enabling automatic updates for minor security releases and performing weekly manual checks for larger feature updates.
- Core Auto-Updates: Enable "Automatic Updates for Maintenance and Security Releases" in your dashboard.
- Plugin Auditing: Immediately remove abandoned plugins that haven't been updated in over 12 months, as they are high-risk entry points.
- Staging Environment Tests: For critical plugins or WooCommerce themes, test the update in a sandbox "staging" site before pushing it to your live Kiwi customers.
- Official Directory Only: Never use "nulled" or pirated versions of premium plugins, as they are almost guaranteed to contain malware backdoors.
Core Auto-Updates: Enable "Automatic Updates for Maintenance and Security Releases" in your dashboard.
Plugin Auditing: Immediately remove abandoned plugins that haven't been updated in over 12 months, as they are high-risk entry points.
Staging Environment Tests: For critical plugins or WooCommerce themes, test the update in a sandbox "staging" site before pushing it to your live Kiwi customers.
Official Directory Only: Never use "nulled" or pirated versions of premium plugins, as they are almost guaranteed to contain malware backdoors.
Cleaning Up Technical Debt
Inactive plugins and themes should be deleted, not just deactivated. Deactivated code still lives on your server and can be exploited by hackers using local file inclusion (LFI) attacks. A lean site is a secure site.
| Update Category | Best Practice | Frequency |
| WP Core | Automatic for minor releases | Instant |
| Security Plugins | Prompt/Instant Updates | Immediate |
| Themes | Manual test on Staging | Weekly |
| Third-Party APIs | Version Monitoring | Monthly |
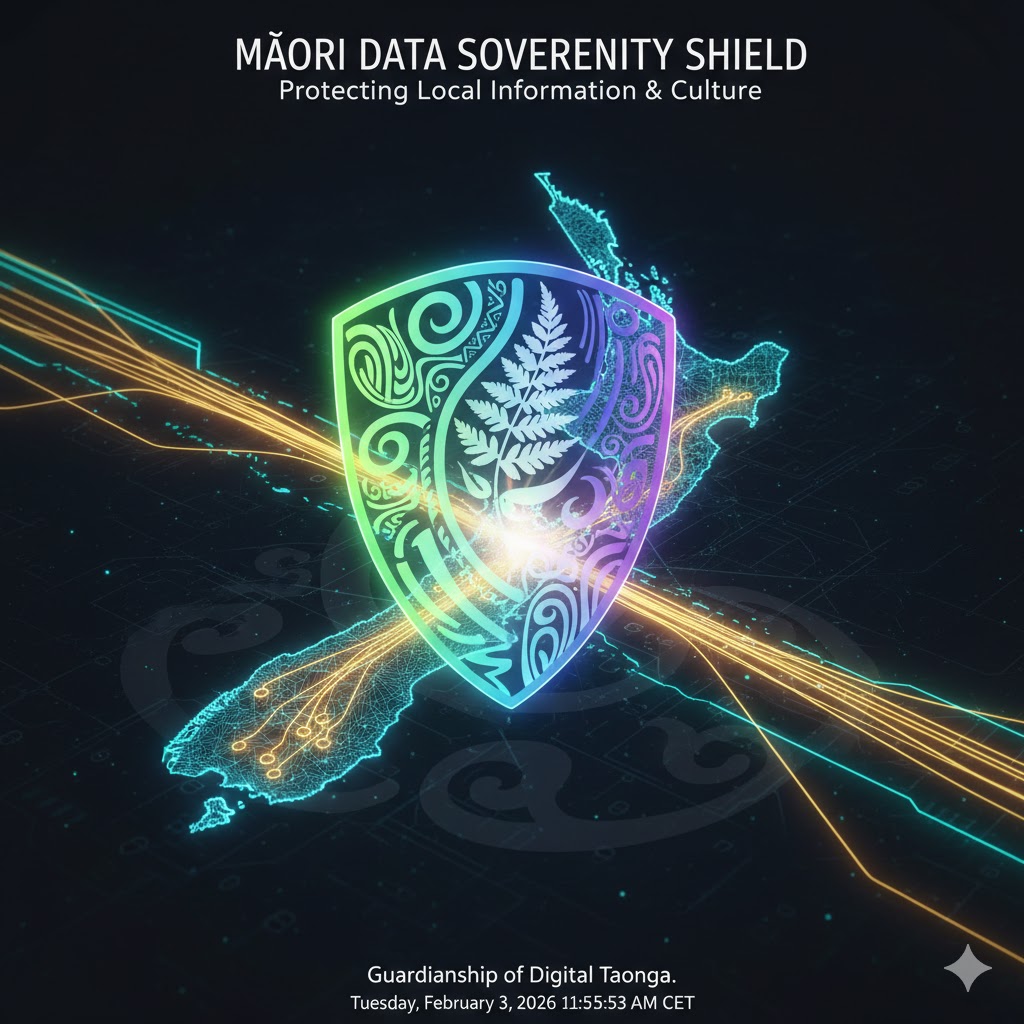
Secure Backups and the "3-2-1" Rule in Aotearoa
Regular backups are your ultimate safety net, but in 2026, ransomware increasingly targets backups first. A secure WordPress hosting security best practices NZ strategy requires more than just a weekly export. You should follow the "3-2-1" rule: maintain at least 3 copies of your data, stored on 2 different types of media, with at least 1 copy kept off-site in a separate physical location (e.g., an independent cloud bucket in a different NZ region).
- Off-Site Redundancy: Storing your backups on a completely different infrastructure from your live site (e.g., Amazon S3, Google Drive, or Dropbox).
- Immutable Backups: Using systems that prevent backup files from being modified or deleted for a set period, protecting against ransomware encryption.
- Retention Policy: Keeping at least 30-90 days of backups to ensure you can revert to a clean version if a hack isn't discovered immediately.
- Restoration Testing: Periodically verifying that you can actually restore your site from a backup; a backup you can't restore is useless.
Off-Site Redundancy: Storing your backups on a completely different infrastructure from your live site (e.g., Amazon S3, Google Drive, or Dropbox).
Immutable Backups: Using systems that prevent backup files from being modified or deleted for a set period, protecting against ransomware encryption.
Retention Policy: Keeping at least 30-90 days of backups to ensure you can revert to a clean version if a hack isn't discovered immediately.
Restoration Testing: Periodically verifying that you can actually restore your site from a backup; a backup you can't restore is useless.
Automated Backup Solutions
Plugins like UpdraftPlus or Jetpack Backup provide easy, automated paths to secure off-site storage. For high-traffic NZ e-commerce sites, hourly or real-time backups are recommended to ensure no customer orders are lost during a recovery event.
Selecting the Right Security Plugins for the NZ Market
While server-level defense is primary, localized security plugins provide the granular control needed for specific NZ business requirements. The best WordPress hosting security best practices NZ involves choosing an "all-in-one" solution like Wordfence or Shield Security PRO that combines firewalls with real-time malware scanning and login hardening. For sites on lower-end hosting, cloud-based options like Sucuri are superior as they perform the heavy security scanning on their own servers, preventing your Auckland-based resources from being consumed during deep scans.
- Wordfence (Best All-Rounder): Features a high-performance endpoint firewall and malware scanner that runs directly on your server.
- Sucuri (Best for High Traffic): Offers an external, cloud-based firewall and CDN that blocks attacks before they reach your NZ host.
- Jetpack Security (Best Multi-Purpose): Ideal for business owners who want integrated backups, downtime monitoring, and spam protection in one package.
- Shield Security PRO (Best AI Defense): Uses advanced AI to repair malicious code automatically and includes "silentCAPTCHA" to block bad bots.
Wordfence (Best All-Rounder): Features a high-performance endpoint firewall and malware scanner that runs directly on your server.
Sucuri (Best for High Traffic): Offers an external, cloud-based firewall and CDN that blocks attacks before they reach your NZ host.
Jetpack Security (Best Multi-Purpose): Ideal for business owners who want integrated backups, downtime monitoring, and spam protection in one package.
Shield Security PRO (Best AI Defense): Uses advanced AI to repair malicious code automatically and includes "silentCAPTCHA" to block bad bots.
| Plugin | Key Advantage | Best For |
| Wordfence | Deep server integration | All-in-one protection |
| Sucuri | Zero performance hit | E-commerce / High traffic |
| Shield PRO | Automated AI Repair | “Hands-off” security |
| All-In-One Security | Totally Free Hardening | Budget-conscious blogs |
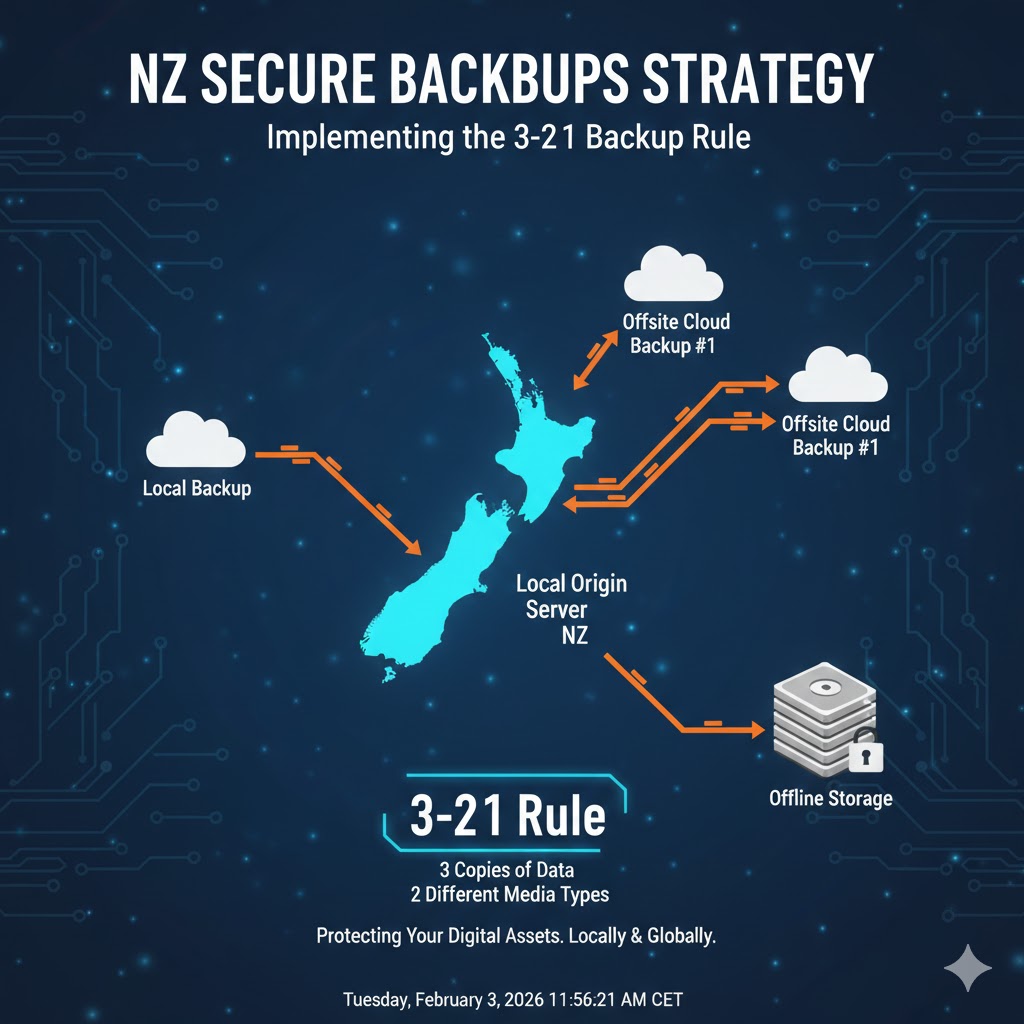
Form Spam and Phishing Defense for Kiwi Customers
Unprotected contact forms are the primary gateway for spam, phishing, and script injection attacks in New Zealand. Malicious actors use automated bots to flood your inbox with fraudulent links that can trick your staff into revealing sensitive business credentials. Implementing "smart filtering" or CAPTCHAs on every form is a mandatory part of WordPress hosting security best practices NZ to maintain the integrity of your customer communication channels.
- Bot-Filtering Plugins: Tools like Akismet or CleanTalk use global databases to identify and block known spam bots before they submit a form.
- Silent CAPTCHAs: Technologies like Google reCAPTCHA v3 or Cloudflare Turnstile block bots without frustrating real Kiwi customers with difficult puzzles.
- File Upload Hardening: If your contact forms allow file uploads (e.g., CVs), ensure they are restricted to specific file types (like PDF) and scanned for viruses instantly.
- SMTP for Email: Use a dedicated SMTP provider (like SendGrid or Mailgun) to ensure your WordPress emails are signed and authenticated, preventing hackers from spoofing your brand.
Bot-Filtering Plugins: Tools like Akismet or CleanTalk use global databases to identify and block known spam bots before they submit a form.
Silent CAPTCHAs: Technologies like Google reCAPTCHA v3 or Cloudflare Turnstile block bots without frustrating real Kiwi customers with difficult puzzles.
File Upload Hardening: If your contact forms allow file uploads (e.g., CVs), ensure they are restricted to specific file types (like PDF) and scanned for viruses instantly.
SMTP for Email: Use a dedicated SMTP provider (like SendGrid or Mailgun) to ensure your WordPress emails are signed and authenticated, preventing hackers from spoofing your brand.
Educating Your Team on Phishing
Even the best technical security can be bypassed by social engineering. Ensure your staff are trained to recognize suspicious requests for passwords or bank details, even if the email appears to come from a "trusted" local source.
Data Privacy by Design: Cookie Compliance and Consent
With the convergence of the NZ Privacy Act and global standards like GDPR, managing how your WordPress site uses cookies is a critical security function. In 2026, WordPress hosting security best practices NZ include implementing "Privacy by Design," where user consent for tracking is obtained before any data is collected. This is particularly important for sites using tracking pixels (Facebook, Google) or personalized advertising, as users must have the legal right to opt-out.
- Transparent Privacy Policies: Every site must have a clear, locally-relevant privacy policy detailing what data is collected and how long it is retained.
- Cookie Consent Banners: Use plugins like Complianz or CookieYes to manage user preferences and provide auto-scanning of your site's cookies.
- Right to Deletion: Ensure your site has a clear path for New Zealand residents to request the access or deletion of their personal information.
- Third-Party Data Sharing: Audit your plugins to see which third parties are receiving data; minimize sharing to only what is strictly necessary.
Transparent Privacy Policies: Every site must have a clear, locally-relevant privacy policy detailing what data is collected and how long it is retained.
Cookie Consent Banners: Use plugins like Complianz or CookieYes to manage user preferences and provide auto-scanning of your site's cookies.
Right to Deletion: Ensure your site has a clear path for New Zealand residents to request the access or deletion of their personal information.
Third-Party Data Sharing: Audit your plugins to see which third parties are receiving data; minimize sharing to only what is strictly necessary.
Simplified Compliance for Tradies and SMEs
Small businesses often feel overwhelmed by privacy laws. Using local hosting and NZ-specific privacy templates simplifies this process, ensuring you earn customer trust without needing a team of lawyers.
Conducting Regular Security Audits and Monitoring
Security is not a one-time setup; it is a continuous process of monitoring and response. A robust WordPress hosting security best practices NZ strategy includes conducting monthly security audits to identify new vulnerabilities or unauthorized user accounts. By reviewing your security logs and file integrity monitoring reports, you can catch silent infections before they damage your SEO rankings or lead to a massive data breach.
- File Integrity Monitoring: Alerts you instantly if core WordPress files are modified unexpectedly, a classic sign of a hack.
- Downtime Monitoring: Using tools like Jetpack or Pingdom to notify you immediately if your site goes offline, allowing for rapid recovery.
- Review User Accounts: Audit your user list monthly and delete any inactive accounts or those with unnecessarily high permissions.
- Audit Logs: Maintaining a record of every login, file change, and plugin update to allow for "digital forensics" after an incident.
File Integrity Monitoring: Alerts you instantly if core WordPress files are modified unexpectedly, a classic sign of a hack.
Downtime Monitoring: Using tools like Jetpack or Pingdom to notify you immediately if your site goes offline, allowing for rapid recovery.
Review User Accounts: Audit your user list monthly and delete any inactive accounts or those with unnecessarily high permissions.
Audit Logs: Maintaining a record of every login, file change, and plugin update to allow for "digital forensics" after an incident.
| Audit Frequency | Task | Tools |
| Weekly | Malware & Vulnerability Scan | Wordfence / MalCare |
| Monthly | User Access & Permissions Audit | Admin dashboard |
| Monthly | Restore Test from Backup | UpdraftPlus / Jetpack |
| Quarterly | Full Security Health Check | Third-party Expert Audit |
When to Call an Expert
If your site is hacked, your immediate actions are critical. While plugins help, complex malware injections are best resolved by WordPress security experts who can perform deep-level file cleaning and ensure no "backdoors" remain in your database.

Final Thoughts
The implementation of WordPress hosting security best practices NZ is the most significant technical investment you can make in your business's longevity. In 2026, a secure site is more than just "hacker-proof"—it is a fast, reliable, and legally compliant platform that respects Māori Data Sovereignty and Kiwi privacy rights. By combining local Auckland-based infrastructure with enforced multi-factor authentication, proactive AI-driven threat detection, and a rigorous update routine, you build a digital fortress that protects your brand's reputation and your customers' trust. In the digital economy of Aotearoa, security is not an expense; it is the foundation of every successful interaction.
For more foundational knowledge on website security, visit the Web Hosting Service Wiki.
Pātai Auau (FAQ)
He aha te painga o te manaaki WordPress ki Aotearoa? The primary benefit is significantly lower latency and full compliance with the NZ Privacy Act 2020. Local hosting ensures your data stays under New Zealand jurisdiction, making it easier to protect sensitive information and meet Māori Data Sovereignty requirements.
Do I really need MFA/2FA for my WordPress admin? Yes. In 2026, passwords alone are insufficient. MFA blocks over 99.9% of account takeovers and is a core requirement for almost any modern security protocol in New Zealand.
Is my customer data more secure if I host in Auckland? Yes, because it is subject to the strict protections of the NZ Privacy Act 2020 and is not inherently subject to foreign surveillance laws like the US CLOUD Act, which can apply to US-owned global clouds even if the server is in NZ.
What is the best security plugin for a Kiwi small business? Wordfence is a highly recommended all-rounder for comprehensive firewall and malware protection. For those wanting a multi-purpose tool, Jetpack Security provides backups, security, and performance in one.
How often should I back up my site? Daily is the minimum baseline for active business sites. For e-commerce stores, real-time or hourly backups are essential to ensure no order data is lost during a recovery.
What are Māori Data Sovereignty principles? These principles advocate for Māori rights and interests in data, emphasizing Māori governance, local storage in Aotearoa, and ensuring data usage benefits Māori communities collectively.
What should I do if my WordPress site is hacked? Immediately take the site offline if necessary, change all passwords, contact your hosting provider, and run a deep malware scan. For complex hacks, hire a WordPress security expert to ensure all backdoors are removed.
Does SSL improve my site's security? Yes, SSL (HTTPS) encrypts the data exchange between your site and your visitors. It is mandatory in 2026 for both security and SEO rankings.
Is "admin" a safe username? No. "Admin" is the first guess in every brute-force attack script. You should always use a unique, non-obvious username for administrative accounts.
How does server location affect my SEO in New Zealand? Google prioritizes page speed. A local server in NZ reduces latency (sub-20ms), which improves your "Core Web Vitals" and can lead to higher rankings in local search results.